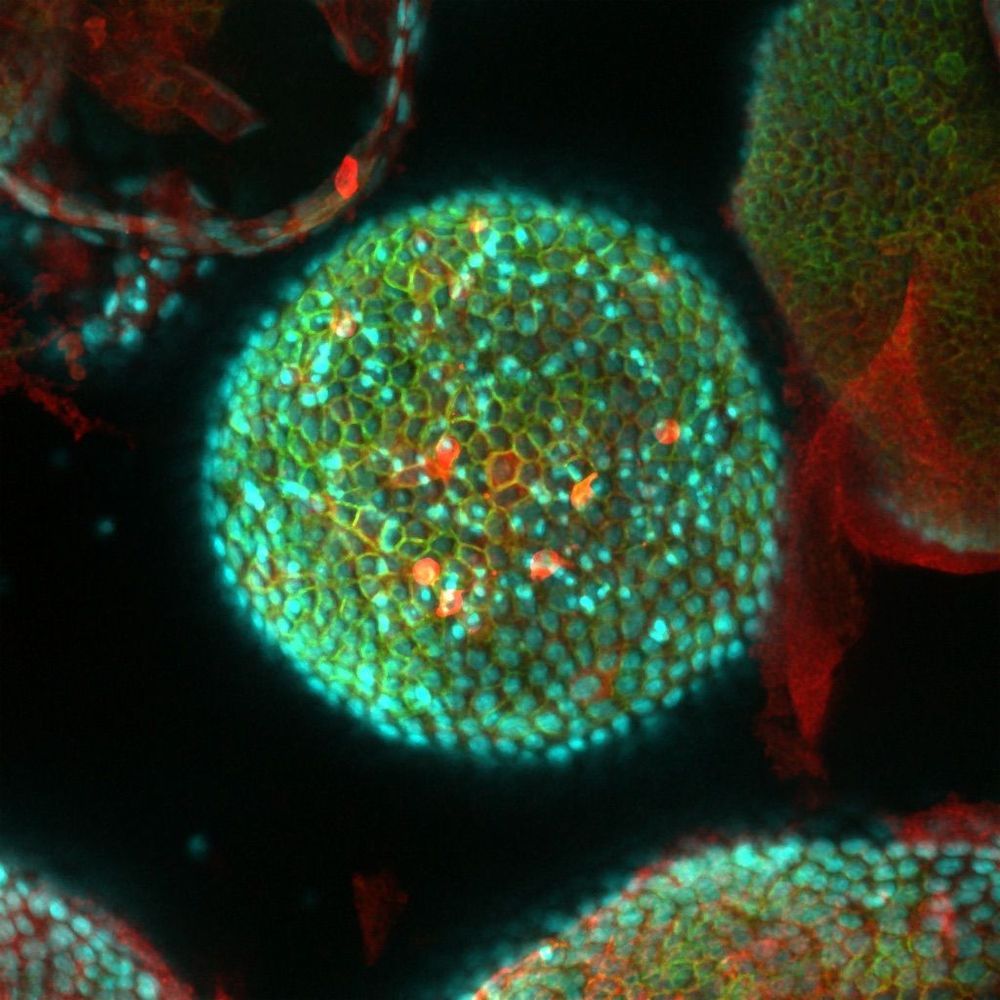
“The team used an advanced imaging technology called “zero-mode waveguide single-molecule fluorescence microscopy,” which they have adapted in recent years for real-time tracking of RNAs and proteins. Ribosomes are made of both RNA and proteins, reflecting a molecular partnership that is widely believed to go back nearly to the dawn of life on Earth.
In a proof-of-principle study published last year, the researchers used their approach to record an early, brief and relatively well-studied stage of ribosome assembly from the bacterium E. coli. This involved the transcription, or copying out from its corresponding gene, of a ribosomal RNA, and initial interactions of this RNA strand with a ribosomal protein.
In the new study, the team extended this approach by tracking not only the transcription of a ribosomal RNA but also its real-time folding. The work provided a detailed look at a complex, and until-now mysterious, part of E. coli ribosome assembly — the formation of an entire major component, or domain, of the E. coli ribosome, with assistance from eight protein partners that end up incorporated into the structure.”
The achievement, reported in Cell, reveals in unprecedented detail how strands of ribonucleic acid (RNA), cellular molecules that are inherently sticky and prone to misfold, are “chaperoned” by ribosomal proteins into folding properly and forming one of the main components of ribosomes.
The findings overturn the longstanding belief that ribosomes are assembled in a tightly controlled, step-wise process.
“In contrast to what had been the dominant theory in the field, we revealed a far more chaotic process,” says James R. Williamson, PhD, a professor in the Department of Integrative Structural & Computational Biology at Scripps Research. “It’s not a sleek Detroit assembly line — it’s more like a trading pit on Wall Street.”