AitM phishing hijacks TikTok Business accounts via Cloudflare Turnstile evasion as SVG malware linked to BianLian targets Venezuela.


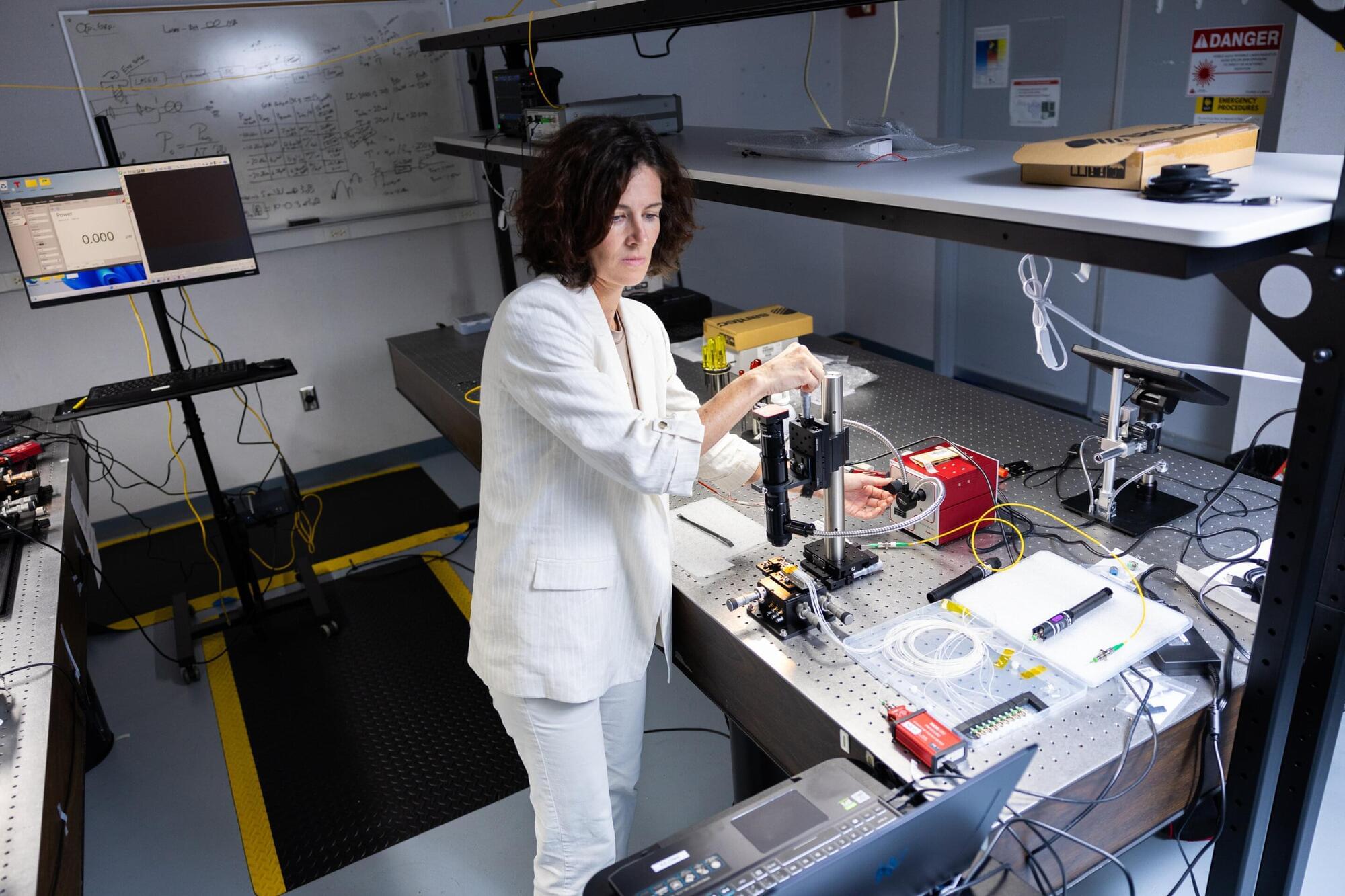
Quantum computing promises to transform our world in rapid, radical and revolutionary ways: solving in seconds problems that would take classical computers years, accelerating the discovery of new medicines, creating sustainable materials, optimizing complex systems, and strengthening cybersecurity. It does so using qubits, the quantum counterparts of classical bits, which can occupy multiple states simultaneously and enable a fundamentally new kind of computation.
For example, imagine 1,000 trucks need to arrive at 10,000 different locations, each, in different parts of the country. A traditional computation model would examine each of the 10 million possible routes one by one to evaluate their efficacy, but a quantum model would be able to evaluate all those millions of different routes instantaneously.
At the same time, quantum sensing is opening new frontiers in precision measurement, enabling technologies such as ultra-sensitive medical imaging and navigation systems that can detect minute changes in gravity or magnetic fields, capabilities that could allow doctors to identify diseases earlier or help vehicles navigate without GPS. UCF researchers believe the science of light, photonics, may hold the key to unlocking quantum computing’s true potential.

Threat actors are targeting TikTok for Business accounts in a phishing campaign that prevents security bots from analyzing malicious pages.
TikTok Business accounts may be targeted due to their high potential for abuse in malvertising campaigns, ad fraud, and the distribution of malicious content.
Browser threat detection and response company Push Security links the campaign to one documented last year, which targeted Google Ad Manager accounts.

A new info-stealing malware called Torg Grabber is stealing sensitive data from 850 browser extensions, more than 700 of them for cryptocurrency wallets.
Initial access is obtained through the ClickFix technique by hijacking the clipboard and tricking the user into executing a malicious PowerShell command.
According to researchers at cybersecurity company Gen Digital, Torg Grabber is actively developed, with 334 unique samples compiled in three months (between December 2025 and February 2026) and new command-and-control (C2) servers registered every week.


Construction, non-profits, real estate, manufacturing, financial services, healthcare, legal, and government are some of the prominent sectors targeted as part of the campaign.
“What also makes this campaign unusual is not just the device code phishing techniques involved, but the variety of techniques observed,” the company said. “Construction bid lures, landing page code generation, DocuSign impersonation, voicemail notifications, and abuse of Microsoft Forms pages are all hitting the same victim pool through the same Railway.com IP infrastructure.”
Device code phishing refers to a technique that exploits the OAuth device authorization flow to grant the attacker persistent access tokens, which can then be used to seize control of victim accounts. What’s significant about this attack method is that the tokens remain valid even after the account’s password is reset.


PTC Inc. is warning of a critical vulnerability in Windchill and FlexPLM, widely used product lifecycle management (PLM) solutions, that could allow remote code execution.
The security issue, identified as CVE-2026–4681, could be leveraged through the deserialization of trusted data.
Its severity has prompted emergency action from German authorities, with the federal police (BKA) reportedly sending agents to affected companies to alert them to the cybersecurity risk.
