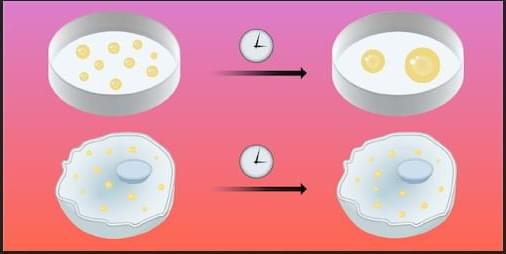
A well-shaken mixture of oil and vinegar will separate as the oil droplets eventually coalesce. Droplet growth, or coarsening, usually evolves according to standard rules. But puzzling exceptions persist. When two polymers are mixed in water and the concentration is high enough, droplets containing one or both species form and can remain stable for hours or days. These loose molecular condensates otherwise behave like liquid droplets, and they abound in biological cells. Now Feipeng Chen of the University of Hong Kong and his colleagues have developed a predictive model for coarsening behavior that works across a range of droplet sizes and explains why coarsening may be suppressed in living systems [1].
The researchers derived their model from observations of a solution containing water and two different polymers, opposite in charge and having very different molecular chain lengths. Using light-scattering techniques, the researchers monitored condensate growth over 12 hours. The initial size and subsequent growth rate of the liquid-like droplets, rich in both polymers, turned out to depend on the solution’s overall initial concentration. In the most dilute solutions, condensates tens-of-nanometers in diameter formed and promptly stopped growing for the remaining 12-hour observation period. In solutions having slightly higher concentration, hundreds-of-nanometer condensates formed and remained stable, then underwent abrupt, rapid growth in the later stages. And in the most concentrated solutions, micrometer-scale condensates formed and grew according to a power-law model.
Applying an electric field to the solutions indicated that the nanoscale condensates had significant surface charge. Modeling these measurements revealed that the asymmetric chain lengths of oppositely charged polymers imparted a net charge to the droplet surfaces. These charges led to size-dependent electrostatic barriers that drastically reduced merging efficiency below a critical diameter. The finding offers a principle for controlling size stability in biology, nanotechnology, and soft-matter assembly.