Chaos ransomware rises after BlackSuit takedown, hitting U.S. targets with $300K demands and stealthy evasion tactics.






Law enforcement has seized the dark web extortion sites of the BlackSuit ransomware operation, which has targeted and breached the networks of hundreds of organizations worldwide over the past several years.
The U.S. Department of Justice confirmed the takedown in an email earlier today, saying the authorities involved in the action executed a court-authorized seizure of the BlackSuit domains.
Earlier today, the websites on the BlackSuit.onion domains were replaced with seizure banners announcing that the ransomware gang’s sites were taken down by the U.S. Homeland Security Investigations federal law enforcement agency as part of a joint international action codenamed Operation Checkmate.

The establishment of a new business park in Killeen is underway.
Wolf Technology Park is set to inhabit 94-acres of real estate located on Texas Highway 195 in south Killeen.
“Wolf Technology Park is a cornerstone of our strategy to attract next-generation employers to Killeen,” Tyler Robert, vice president of the Killeen Economic Development Corporation, said. “With infrastructure investments already in place and sites ready for development, the park is well-positioned to support advanced manufacturing, federal services, health and life sciences, research and development, cybersecurity and semiconductor-related industries.”

TOI Tech Desk’s news coverage spans a wide spectrum across gadget launches, gadget reviews, trends, in-depth analysis, exclusive reports and breaking stories that impact technology and the digital universe. Be it how-tos or the latest happenings in AI, cybersecurity, personal gadgets, platforms like WhatsApp, Instagram, Facebook and more; TOI Tech Desk brings the news with accuracy and authenticity.


Threat hunters have disclosed two different malware campaigns that have targeted vulnerabilities and misconfigurations across cloud environments to deliver cryptocurrency miners.
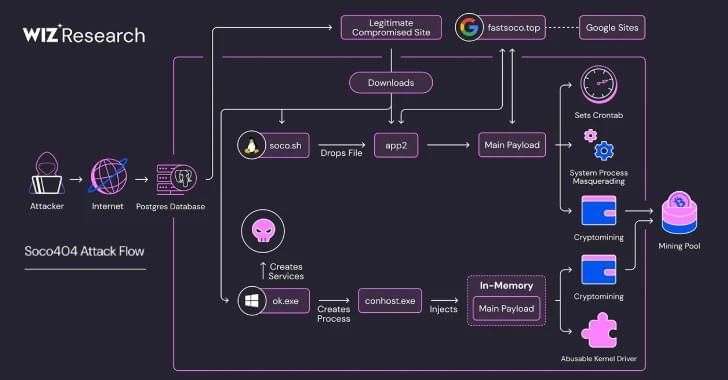
The threat activity clusters have been codenamed Soco404 and Koske by cloud security firms Wiz and Aqua, respectively.
Soco404 “targets both Linux and Windows systems, deploying platform-specific malware,” Wiz researchers Maor Dokhanian, Shahar Dorfman, and Avigayil Mechtinger said. “They use process masquerading to disguise malicious activity as legitimate system processes.”