Mandatory scanning of our private chats might be coming next


New 2TETRA:2BURST flaws expose TETRA networks to injection, replay, and brute-force risks. Critical for public safety.
Veteran cryonicist and inventor of cryptographic hashing, Ralph Merkle, tells us how he came to decide that cryonics was a good idea. In his talk, Ralph discusses Information Theoretic Death, why information is so hard to destroy, and how advances in nano-tech might make cryonics revival possible.
Links:
• Cryosphere Discord server: https://discord.com/invite/ndshSfQwqz.
• Cryonics subreddit: https://www.reddit.com/r/cryonics/
#cryosphere



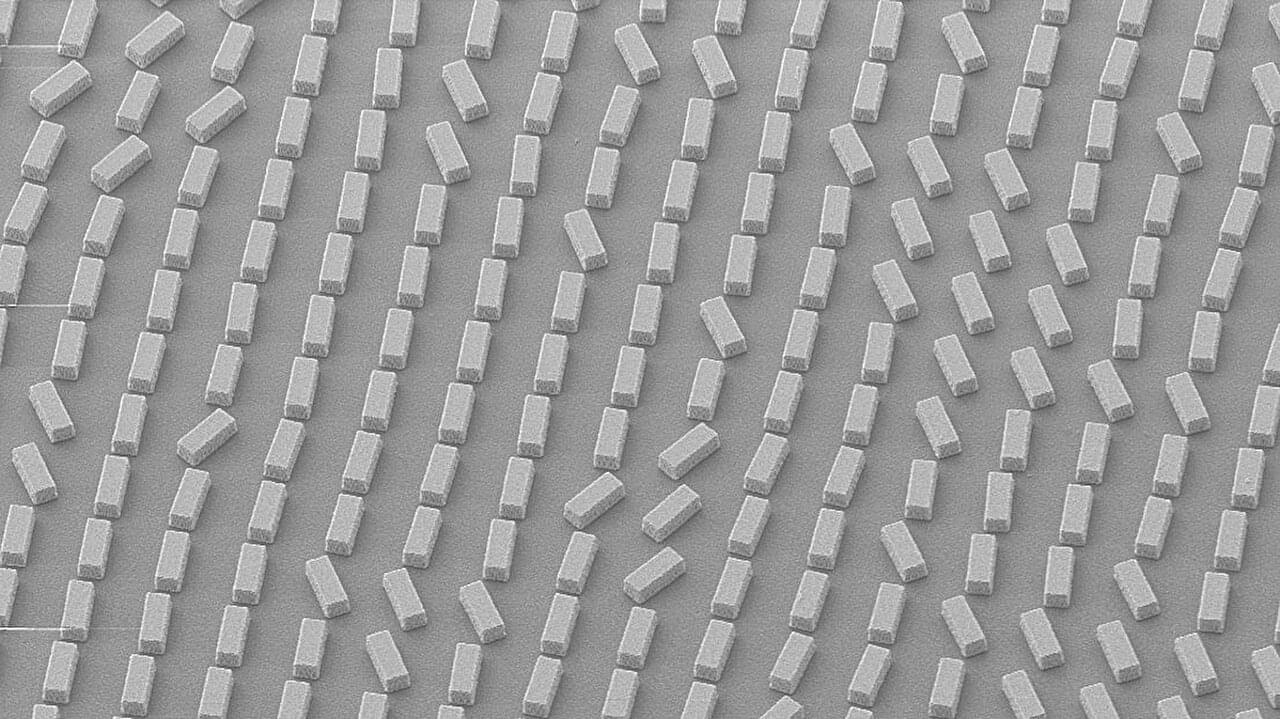
In 2024, a quantum state of light was successfully teleported through more than 30 kilometers (around 18 miles) of fiber optic cable amid a torrent of internet traffic – a feat of engineering once considered impossible.
The impressive demonstration by researchers in the US may not help you beam to work to beat the morning traffic, or download your favourite cat videos faster.
However, the ability to teleport quantum states through existing infrastructure represents a monumental step towards achieving a quantum-connected computing network, enhanced encryption, or powerful new methods of sensing.
Experts say quantum computing is the future of computers. Unlike conventional computers, quantum computers leverage the properties of quantum physics such as superposition and interference, theoretically outperforming current equipment to an exponential degree.
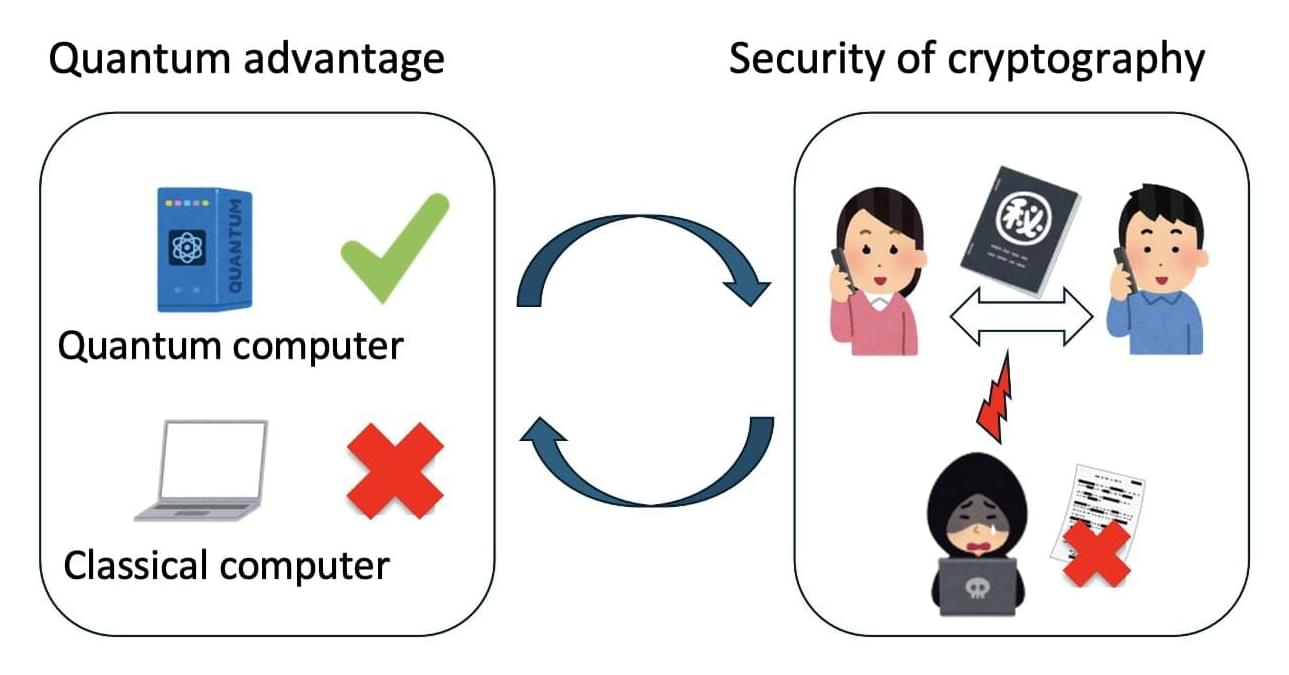
When a quantum computer is able to solve a problem unfeasible for current technologies, this is called the “quantum advantage.” However, this edge is not guaranteed for all calculations, raising fundamental questions regarding the conditions under which such an advantage exists. While previous studies have proposed various sufficient conditions for quantum advantage, the necessity of these conditions has remained unclear.
Motivated by this uncertainty, a team of researchers at Kyoto University has endeavored to understand the necessary and sufficient conditions for quantum advantage, using an approach combining techniques from quantum computing and cryptography, the science of coding information securely.

An international law enforcement action dismantled a Romanian ransomware gang known as ‘Diskstation,’ which encrypted the systems of several companies in the Lombardy region, paralyzing their businesses.
The law enforcement operation codenamed ‘Operation Elicius’ was coordinated by Europol and also involved police forces in France and Romania.
Diskstation is a ransomware operation that targets Synology Network-Attached Storage (NAS) devices, which are commonly used by companies for centralized file storage and sharing, data backup and recovery, and general content hosting.