Particle detectors play a crucial role in our understanding of the fundamental building blocks of the universe. They allow scientists to study the behavior and properties of the particles produced in high-energy collisions. Such particles are boosted to near the speed of light in large accelerators and then smashed into targets or other particles where they are then analyzed with detectors. Traditional detectors, however, lack the needed sensitivity and precision for certain types of research.
Researchers at the U.S. Department of Energy’s (DOE) Argonne National Laboratory have made a significant breakthrough in the field of high-energy particle detection in recent experiments conducted at the Test Beam Facility at DOE’s Fermi National Accelerator Laboratory (Fermilab).
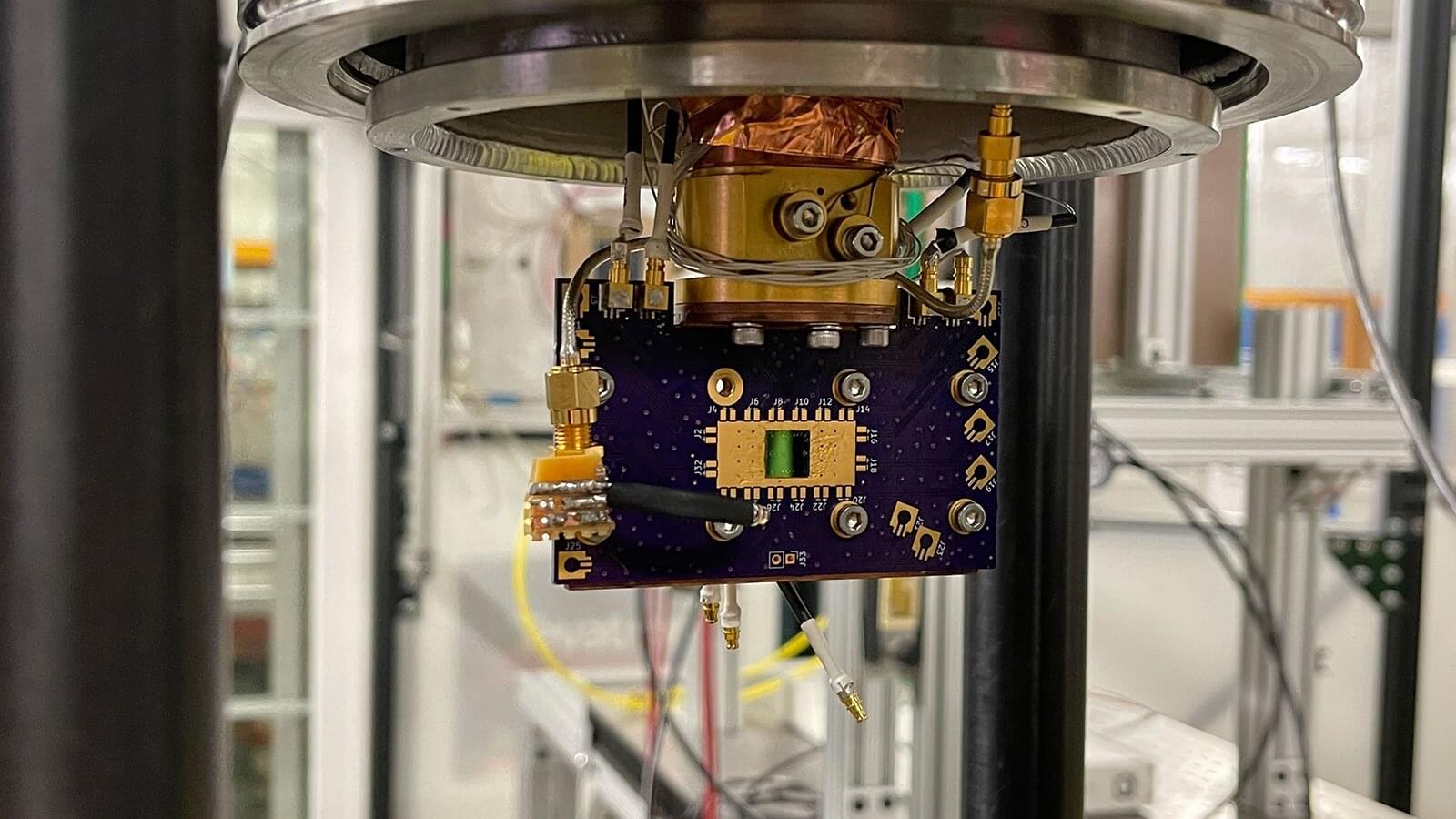
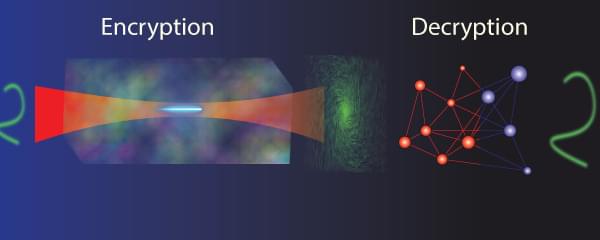
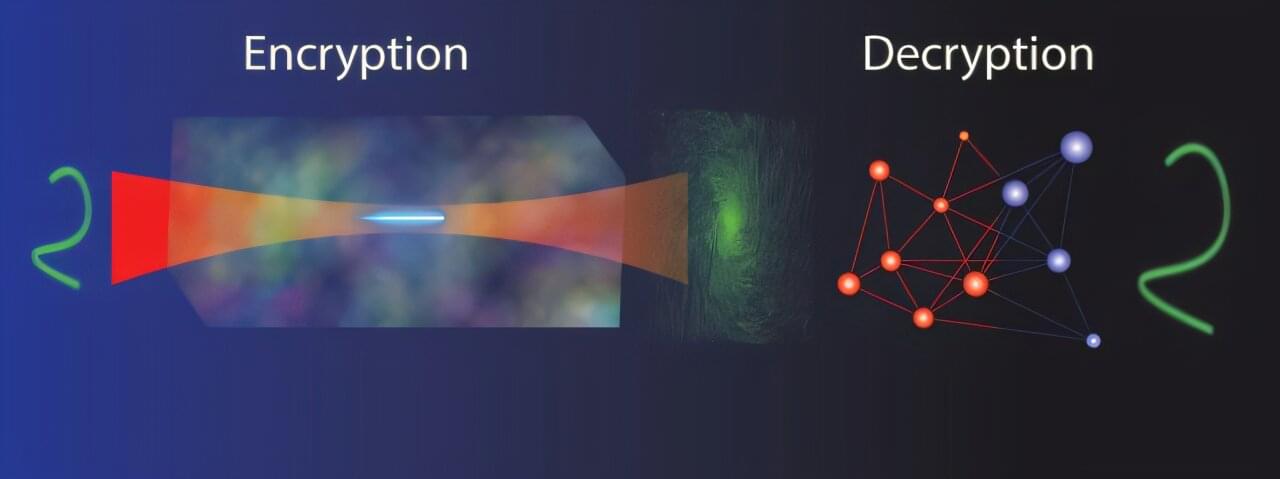
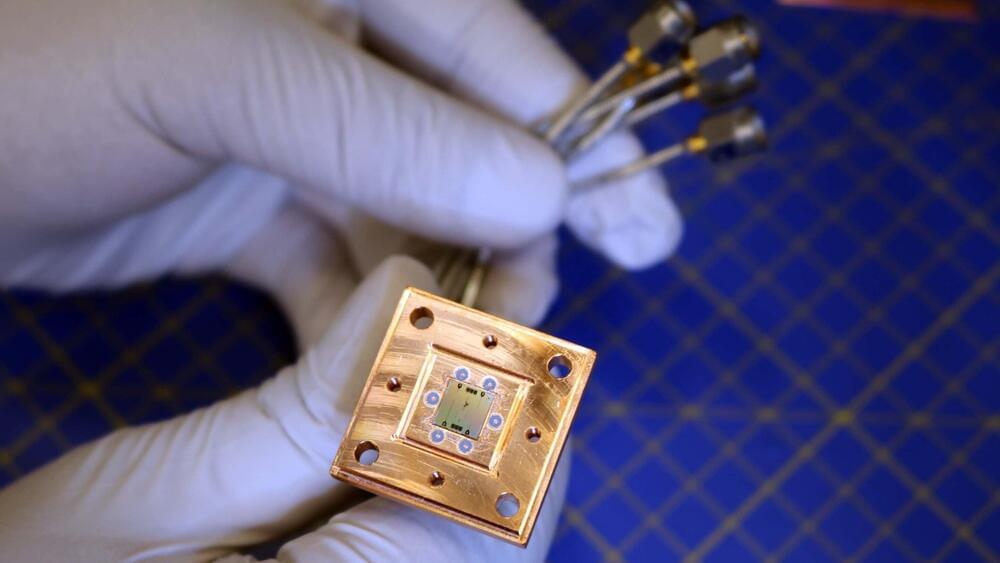
They have found a new use for the superconducting nanowire photon detectors (SNSPDs) already employed for detecting photons, the fundamental particles of light. These incredibly sensitive and precise detectors work by absorbing individual photons. The absorption generates small electrical changes in the superconducting nanowires at very low temperatures, allowing for the detection and measurement of photons. Specialized devices able to detect individual photons are crucial for quantum cryptography (the science of keeping information secret and secure), advanced optical sensing (precision measurement using light) and quantum computing.