The 41-year-old computing method can decode encrypted messages and help detect hidden military vehicles such as stealth aircraft.

James McKenzie is excited about the prospects of firms that are developing technology based on seemingly esoteric fundamental quantum phenomena.
Physicists have long boasted of their success in what’s known as “quantum 1.0” technology – semiconductor junctions, transistors, lasers and so on. Thanks to their efforts over the last 75 years, we have smart phones, computers, laptops and other quantum-enabled devices that have transformed our lives. But the future will increasingly depend on “quantum 2.0” technology, which taps into phenomena like superposition and entanglement to permit everything from quantum computing and cryptography to quantum sensing, timing and imaging.
The incredible possibilities of quantum 2.0 were brought home to me when I attended the UK’s National Quantum Technologies Showcase in central London last month. The event featured more than 60 exhibitors and I was amazed how far things have progressed. In fact, it coincided with two positive developments. One was an announcement by UK Research and Innovation (UKRI) of a further £50m to support quantum industrial projects. The other was the UK and US signing a joint “statement of intent” to boost collaboration on quantum science and technologies.
While they wrestle with the immediate danger posed by hackers today, US government officials are preparing for another, longer-term threat: attackers who are collecting sensitive, encrypted data now in the hope that they’ll be able to unlock it at some point in the future.
The threat comes from quantum computers, which work very differently from the classical computers we use today. Instead of the traditional bits made of 1s and 0s, they use quantum bits that can represent different values at the same time. The complexity of quantum computers could make them much faster at certain tasks, allowing them to solve problems that remain practically impossible for modern machines—including breaking many of the encryption algorithms currently used to protect sensitive data such as personal, trade, and state secrets.
While quantum computers are still in their infancy, incredibly expensive and fraught with problems, officials say efforts to protect the country from this long-term danger need to begin right now.

This week, Amazon’s Web Services (AWS) kicked off its tenth re: Invent conference, an event where it typically announces the biggest changes in the cloud computing industry’s dominant platform. This year’s news includes faster chips, more aggressive artificial intelligence, more developer-friendly tools, and even a bit of quantum computing for those who want to explore its ever-growing potential.
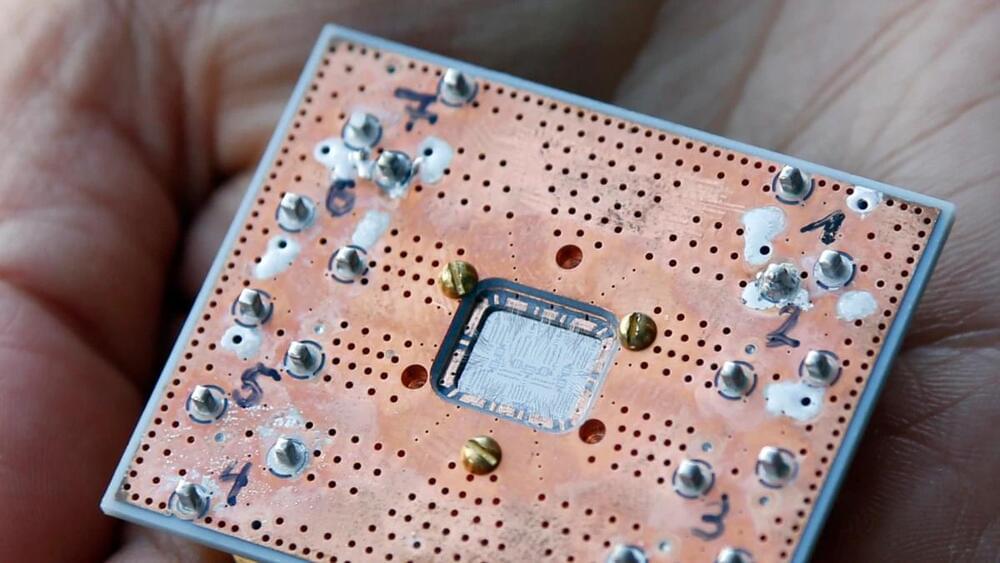
Amazon is working to lower costs by boosting the performance of its hardware. Their new generation of machines powered by the third generation of AMD’s EPYC processors, the M6a, is touted as offering a 35% boost in price/performance over the previous generation of M5a machines built with the second generation of the EPYC chips. They’ll be available in sizes that range from two virtual CPUs with 8GB of RAM (m6a.large) up to 192 virtual CPUs and 768GB of RAM (m6a.48xlarge).
AWS also notes that the chips will boast “always-on memory encryption” and rely on faster custom circuitry for faster encryption and decryption. The feature is a nod to users who worry about sharing hardware in the cloud and, perhaps, exposing their data.

Using a focused laser beam, scientists can manipulate properties of nanomaterials, thus ‘writing’ information onto monolayer materials. By this means, the thinnest light disk at atomic level was demonstrated.
The bottleneck in atomic-scale data storage area may be broken by a simple technique, thanks to recent innovative studies conducted by scientists from Nanjing Normal University (NJNU) and Southeast University (SEU).
Through a simple, efficient and low-cost technique involving the focused laser beam and ozone treatment, the NJNU and SEU research teams, leading by Prof. Hongwei Liu, Prof. Junpeng Lu and Prof. Zhenhua Ni demonstrated that the photoluminescence (PL) emission of WS2 monolayers can be controlled and modified, and consequently, it works as the thinnest light disk with rewritable data storage and encryption capability.

At the conference, Science History Institute postdoctoral researcher Megan Piorko presented a curious manuscript belonging to English alchemists John Dee (1527–1608) and his son Arthur Dee (1579–1651). In the pre-modern world, alchemy was a means to understand nature through ancient secret knowledge and chemical experiment.
Within Dee’s alchemical manuscript was a cipher table, followed by encrypted ciphertext under the heading “Hermeticae Philosophiae medulla”—or Marrow of the Hermetic Philosophy. The table would end up being a valuable tool in decrypting the cipher, but could only be interpreted correctly once the hidden “key” was found.
It was during post-conference drinks in a dimly lit bar that Megan decided to investigate the mysterious alchemical cipher—with the help of her colleague, University of Graz postdoctoral researcher Sarah Lang.

There’s a lot of excitement at the intersection of artificial intelligence and health care. AI has already been used to improve disease treatment and detection, discover promising new drugs, identify links between genes and diseases, and more.
By analyzing large datasets and finding patterns, virtually any new algorithm has the potential to help patients — AI researchers just need access to the right data to train and test those algorithms. Hospitals, understandably, are hesitant to share sensitive patient information with research teams. When they do share data, it’s difficult to verify that researchers are only using the data they need and deleting it after they’re done.
Secure AI Labs (SAIL) is addressing those problems with a technology that lets AI algorithms run on encrypted datasets that never leave the data owner’s system. Health care organizations can control how their datasets are used, while researchers can protect the confidentiality of their models and search queries. Neither party needs to see the data or the model to collaborate.