A tiny device that entangles light and electrons without super-cooling could revolutionize quantum tech in cryptography, computing, and AI.
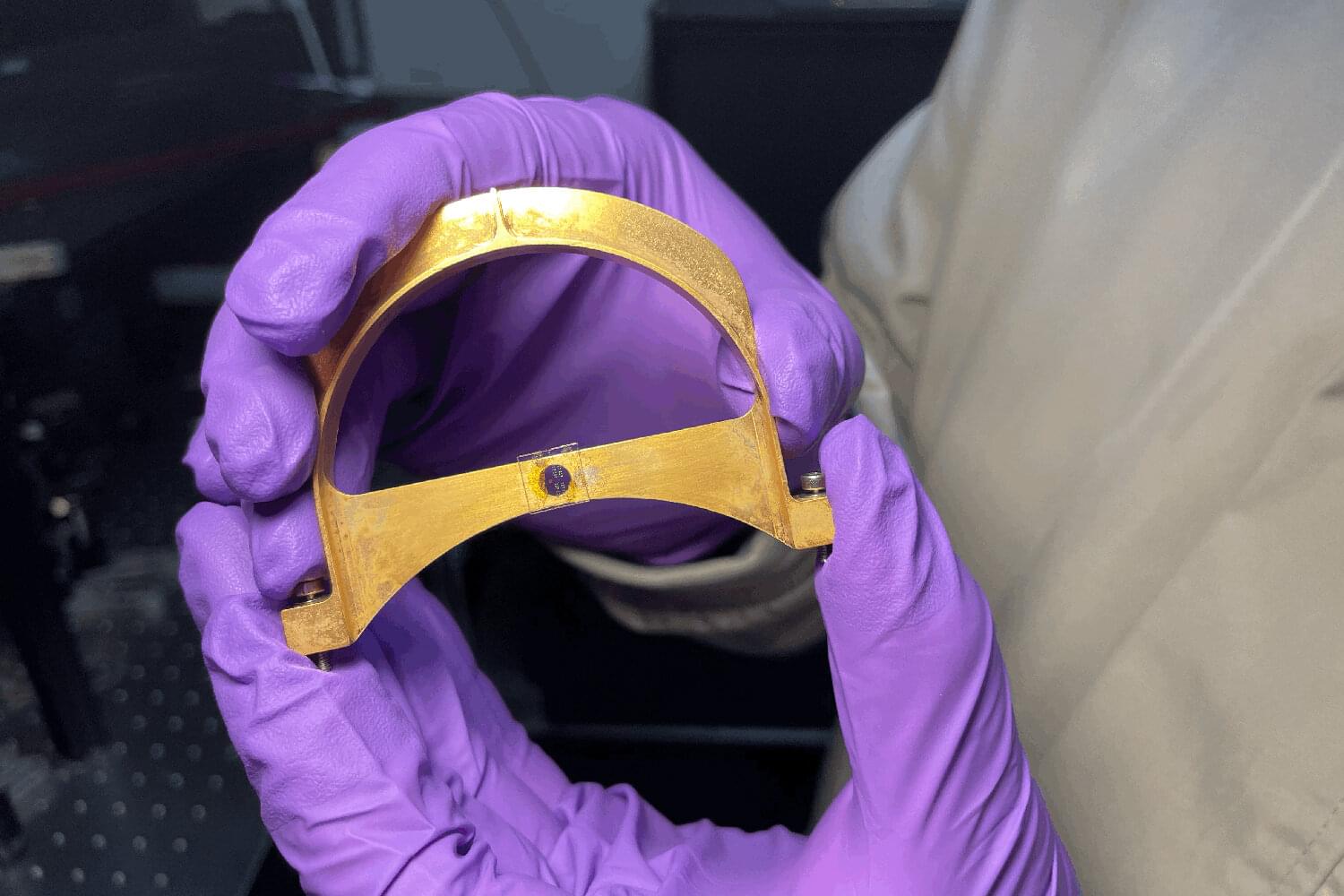
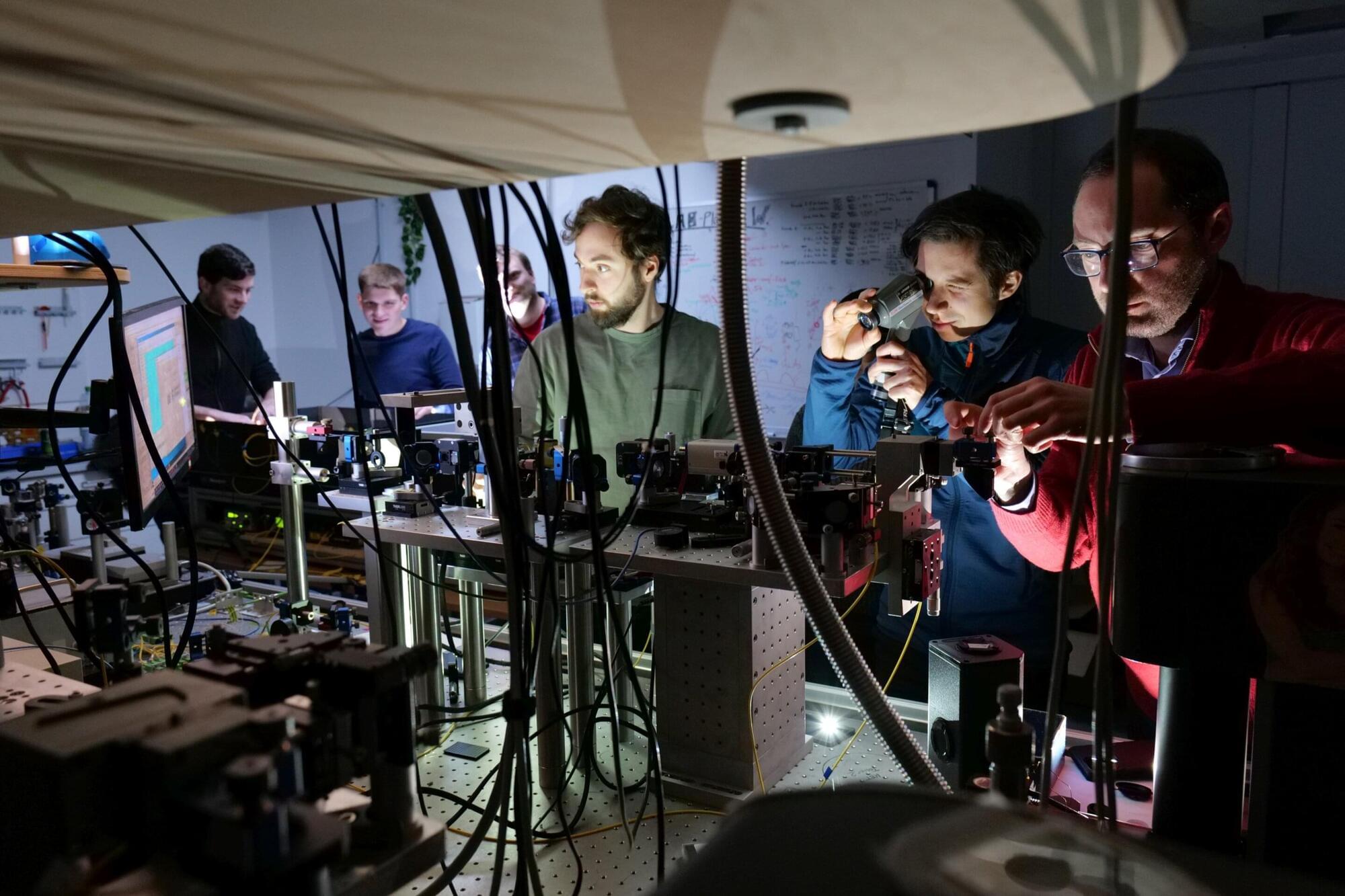
Present-day quantum computers are big, expensive, and impractical, operating at temperatures near-459 degrees Fahrenheit, or “absolute zero.” In a new paper, however, materials scientists at Stanford University introduce a new nanoscale optical device that works at room temperature to entangle the spin of photons (particles of light) and electrons to achieve quantum communication—an approach that uses the laws of quantum physics to transmit and process data. The technology could usher in a new era of low-cost, low-energy quantum components able to communicate over great distances.
“The material in question is not really new, but the way we use it is,” says Jennifer Dionne, a professor of materials science and engineering and senior author of the paper just published in Nature Communications describing the novel device. “It provides a very versatile, stable spin connection between electrons and photons that is the theoretical basis of quantum communication. Typically, however, the electrons lose their spin too quickly to be useful.”