To revist this article, visit My Profile, then View saved stories.


To revist this article, visit My Profile, then View saved stories.

The FBI and NSA issue joint security alert containing technical details about new Linux malware developed by Russia’s military hackers.

Biometrics may be the best way to protect society against the threat of deepfakes, but new solutions are being proposed by the Content Authority Initiative and the AI Foundation.
Deepfakes are the most serious criminal threat posed by artificial intelligence, according to a new report funded by the Dawes Centre for Future Crime at the University College London (UCL), among a list of the top 20 worries for criminal facilitation in the next 15 years.
The study is published in the journal Crime Science, and ranks the 20 AI-enabled crimes based on the harm they could cause.
On the higher end, they work to ensure that development is open in order to work on multiple cloud infrastructures, providing companies the ability to know that portability exists.
That openness is also why deep learning is not yet part of a solution. There is still not the transparency needed into the DL layers in order to have the trust necessary for privacy concerns. Rather, these systems aim to help manage information privacy for machine learning applications.
Artificial intelligence applications are not open, and can put privacy at risk. The addition of good tools to address privacy for data being used by AI systems is an important early step in adding trust into the AI equation.

A security expert revealed this week that an exploit commonly used against Windows users who own Microsoft Office can sneak into MacOS systems as well.
A former NSA security specialist who addressed the Black Hat security conference this week summarized his research into the new use for a very old exploit.
Patrick Wardle explained that the exploit capitalizes on the use of macros in Microsoft Office. Hackers have long used the approach to trick users into granting permission to activate the macros, which in turn surreptitiously launch malicious code.
Consumers are ending up increasingly responsive about sharing their data, as data integrity and security has turned into a developing concern. In any case, with the advent of nations teching up with facial recognition, even explorers need to truly begin thinking about what sort of data they could be reluctantly offering to nations, individuals and places.
Facial recognition innovation is a framework that is fit for identifying or confirming an individual from an advanced picture or a video frame. It works by comparing chosen facial highlights and faces inside a database. The technology is utilized in security frameworks and can be compared with different biometrics, for example, fingerprint or iris recognition frameworks. As of late, it has been grabbed and utilized as a business identification and advertising tool. The vast majority have a cell phone camera fit for recognizing features to perform exercises, for example, opening said a cell phone or making payments.
The worldwide market for facial recognition cameras and programming will be worth of an expected $7.8 billion, predicts Markets and Markets. Never again consigned to sci-fi films and books, the technology is being used in various vertical markets, from helping banks recognize clients to empowering governments to look out for criminals. Let’s look at some of the top countries adopting facial recognition technology.

Google has begun rolling out a feature that allows you to configure how long it can save data from all of the Google services you use, like maps, search and everything you do online. Until now, you had to manually delete this data or turn it off entirely. Deleting it means Google doesn’t always have enough information about you to make recommendations on what it thinks you’ll like, or where you might want to go.
Now, you can tell Google to automatically delete personal information after three months or 18 months. Here’s how you can do that.
Google has a new feature that will automatically delete the data it has on how you use its apps and what you do on the web.
Digital identity capabilities from Trust Stamp are now being integrated with Mastercard’s Wellness Pass solution, which it will launch in cooperation with Gavi in West Africa. Proving identity without revealing any information about it is the idea behind Trust Stamp’s zero knowledge approach to online identity verification, according to a profile by Mastercard.
Gareth Genner, Trust Stamp co-founder and CEO, explains in an interview how the company’s Evergreen Hash technology uses biometrics without taking on the risk of spoofing or a data breach that he says come with standard biometric implementations.
The Evergreen Hash is created from the customers face, palm or fingerprint biometrics, which the company uses to generate a “3D mask,” discarding raw data and adding encryption to associate the data with the user.
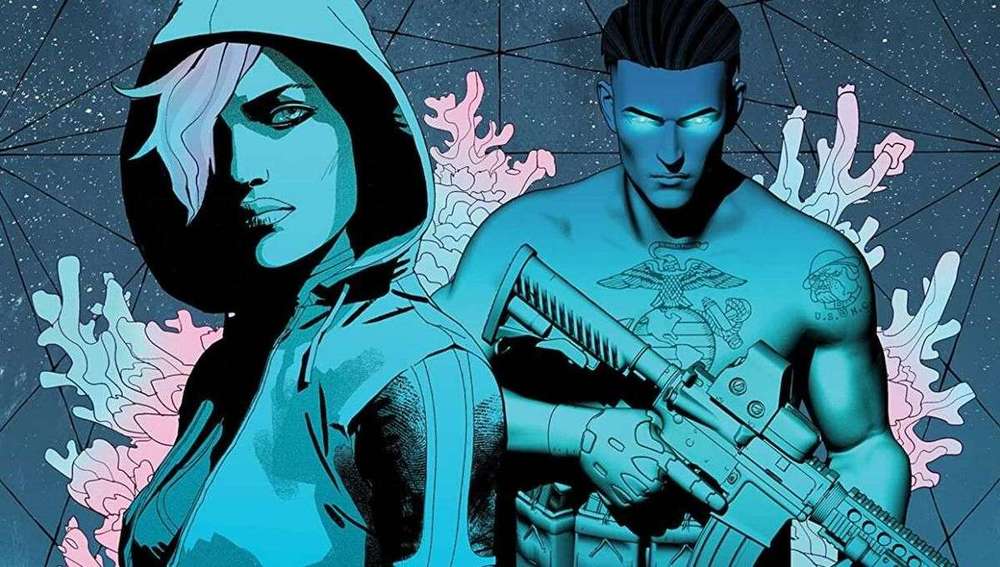
Sable co-created the story with artist Kristian Donaldson (Unthinkable, The Guild) and Mey Rude, a transgender woman who served as a consulting editor on the project. Sable took some time to talk to SYFY WIRE about biohacking, transhumanism, and how science fiction often predicts the future.
The Dark, by screenwriter and playwright Mark Sable (Unthinkable, Godkillers), is a graphic novel about a world plunged into chaos when a biotech virus pulls everything offline. The plot twists around government conspiracies, techno warfare, biohacking, and the unlikely pair out to stop it before another world war breaks loose. To make it all the scarier, Sable bases his fiction on fact. As a futurist who has consulted with think tanks and The Art of Future Warfare Project, he is well versed in techno warfare scenarios.
The Dark begins in 2035 and follows Master Sergeant Robert Carter, a N.E.O. (Networked Exoskeleton Operator) Marine whose power armor links him to the world’s technology, and whose implants mentally connect him to his unit. He feels what they feel, which proves torturous when his unit is attacked. The Dark takes on a double meaning as the experience leaves him both physically and technologically blind as the world’s tech crashes.
His world changes when he is sent after Camille — a skilled biohacker and analyst for NSA’s Bumble Hive — who is on a mission to expose the government’s use of bio-hacked surveillance. But she’s also attempting to recode herself in the process. You see, Camille is a trans woman and has discovered a way to change her gender at the molecular level. Camille’s quest to expose the truth and Carter’s pursuit of that very truth throw them together in a race against time to save the world.