In Brief.
- Data can be sent at rates of 50 bps on laptop touchpads and 25 bps with fingerprint sensors using on-body transmission.
- New developments in biometrics are allowing for even greater privacy and security in our networked society.

As useful as they are, wearable fitness trackers aren’t usually the height of fashion themselves, with many devices blending away out of sight on your wrist or ankle. Now Intel and Luxottica have teamed up to put a fitness tracker front and center on your face, stashing various biometric sensors and a voice-activated AI coach into a stylish, custom-designed pair of Oakley shades.

Ouch!!!
National Security Agency says tools left exposed by mistake — and dumping by presumably Russia-backed hackers Shadow Brokers.
An FBI investigation into the public dumping of hacking tools used by the National Security Agency (NSA) to uncover security flaws in some networking vendor products is looking at how the tools were exposed on a remote computer, a Reuters report says, quoting people close to the investigation.
Sources say NSA believes it was an inadvertent act by an employee or contractor, but the NSA did not inform manufacturers of the leak because sensors employed to detect misuse of the tools came up empty-handed. NSA may have wanted to take advantage of the theft to gather intelligence and improve its defense, adds the exclusive.


Interesting read on IPC Systems Inc. is partnering with U.K. startup Post-Quantum to (in their own words) “offer its clients encryption, biometric authentication and a distributed-ledger record-keeping system that the software company says is designed to resist hacking — even by a quantum computer.” — I will be researching this more.
(Bloomberg) — When it comes to cybersecurity, no one can accuse IPC Systems Inc., the New Jersey-based company that builds communications networks for trading firms and financial markets, of preparing to fight the last war.

Hope they’re working with QC researchers in Los Alamos and DARPA; it is the US Government which is known for its silos and multi-layer bureaucracies.
Quantum computing is a novel way to build computers — one that takes advantage of the quantum properties of particles to perform operations on data in a very different way than traditional computers. In some cases, the algorithm speedups are extraordinary.
Specifically, a quantum computer using something called Shor’s algorithm can efficiently factor numbers, breaking RSA. A variant can break Diffie-Hellman and other discrete log-based cryptosystems, including those that use elliptic curves. This could potentially render all modern public-key algorithms insecure. Before you panic, note that the largest number to date that has been factored by a quantum computer is 143. So while a practical quantum computer is still science fiction, it’s not stupid science fiction.
(Note that this is completely different from quantum cryptography, which is a way of passing bits between two parties that relies on physical quantum properties for security. The only thing quantum computation and quantum cryptography have to do with each other is their first words. It is also completely different from the NSA’s QUANTUM program, which is its code name for a packet-injection system that works directly in the Internet backbone.)


A day in the life of an NSA Hacker.
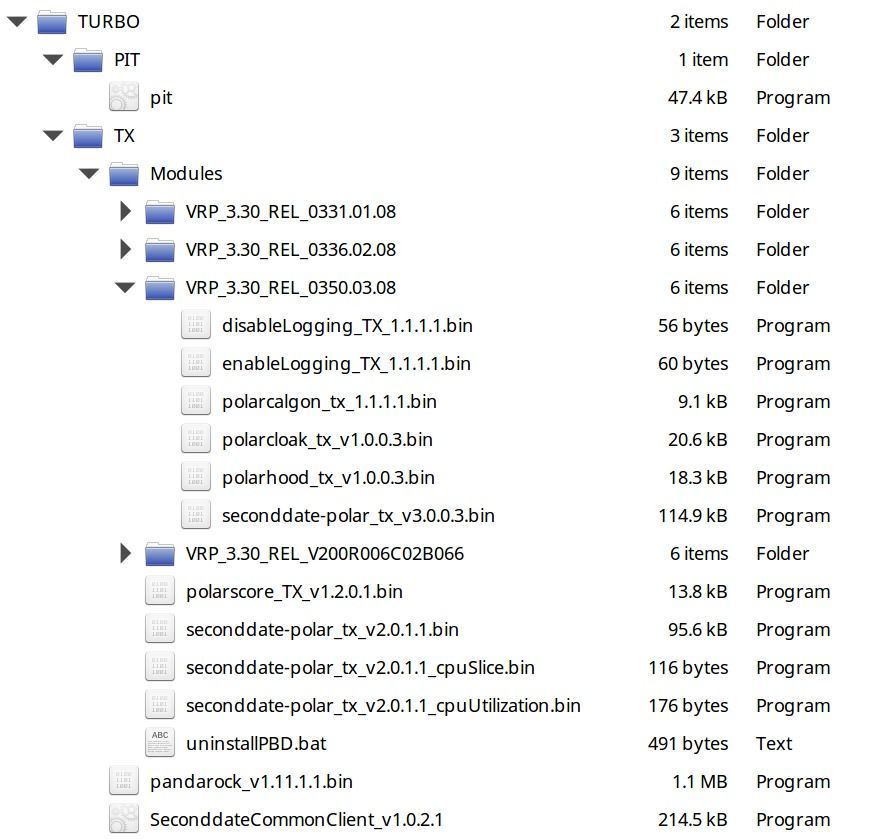
In what Edward Snowden deems “not unprecedented,” hackers calling themselves the Shadow Brokers have collected NSA-created malware from a staging server run by the Equation Group, an internal hacking team. The Shadow Brokers published two chunks of data, one “open” chunk and another encrypted file containing the “best files” that they will sell for at least $1 million. Wikileaks has said they already own the “auction” files and will publish them in “due course.”
They’ve also released images of the file tree containing a script kiddie-like trove of exploits ostensibly created and used by the NSA as well as a page calling out cyber warriors and “Wealthy Elites.” The page also contains links to the two files, both encrypted. You can grab them using BitTorrent here.

Like this article; there is 2 more pieces missing from the roadmap for 2010 & beyond and that is Biocomputing & Singularity. Biocomputing will provide the financial industry (banks, trading firms, accounting & audit firms, bond insurers, etc.) the ability to expand information/ data storage and transmission capacities like we have never see before just look at what Microsoft, Google, Amazon, etc. have done with DNA storage. And, the much loved Singularity enables boosting of knowledge and insights as well as more mobility and access to information as they need it. BTW — Biometrics is NOT the same as Biocomputing; biocomputing goes well beyond security/ identity management.
The influential non-profit rates these technologies alongside the PC, the internet, and smartphones in terms of their potential to transform financial…
