This website uses a security service to protect against malicious bots. This page is displayed while the website verifies you are not a bot.


Anthropic appears to be preparing for the public rollout of “Mythos,” which was announced in April as a restricted model that poses major security risks to private and public software.
On April 7, Anthropic announced the Mythos in early preview and called it a new frontier model with strikingly advanced capabilities in computer security tasks.
Anthropic said the Mythos model shows major improvements in code reasoning and autonomy, far above its current flagship model, Opus 4.7.
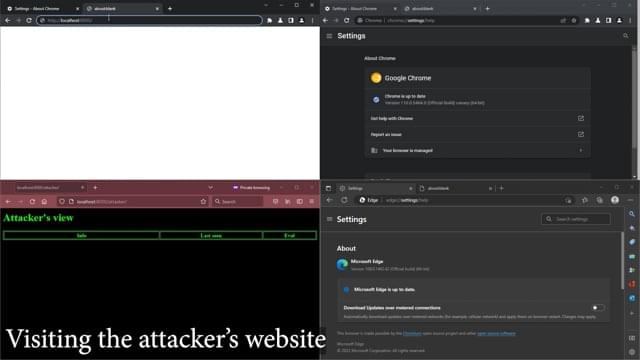
Google has accidentally leaked details about an unfixed issue in Chromium that keeps JavaScript running in the background even when the browser is closed, allowing remote code execution on the device.
The flaw was reported by security researcher Lyra Rebane and acknowledged as valid in December 2022, as per the thread on Chromium Issue Tracker.
An attacker could exploit the problem to create a malicious webpage with a Service Worker, such as a download task, that never terminates. Rebane says that this could allow an attacker to execute JavaScript code on the visitors’ devices.

Drupal has released security updates for a “highly critical” security vulnerability in Drupal Core that could be exploited by attackers to achieve remote code execution, privilege escalation, or information disclosure.
The vulnerability, now tracked as CVE-2026–9082, carries a CVSS score of 6.5 out of 10.0, per CVE.org. Drupal said the vulnerability resides in a database abstraction API that is used in Drupal Core to validate queries and ensure they are sanitized against SQL injection attacks.
“A vulnerability in this API allows an attacker to send specially crafted requests, resulting in arbitrary SQL injection for sites using PostgreSQL databases,” it said. “This can lead to information disclosure, and in some cases privilege escalation, remote code execution, or other attacks.”
Microsoft has shared mitigations for YellowKey, a recently disclosed Windows BitLocker zero-day vulnerability that grants access to protected drives.
The security flaw was disclosed last week by an anonymous security researcher known as ‘Nightmare Eclipse,’ who described it as a backdoor and published a proof-of-concept (PoC) exploit.
Nightmare Eclipse said that exploiting this zero-day involves placing specially crafted ‘FsTx’ files on a USB drive or EFI partition, rebooting into WinRE, and then triggering a shell with unrestricted access to the BitLocker-protected storage volume by holding down the CTRL key.
A recently patched Linux privilege escalation vulnerability now has a publicly available proof-of-concept (PoC) exploit that allows local attackers to gain root privileges on Arch Linux systems.
The vulnerability, named PinTheft by the V12 security team and still waiting to be assigned a CVE ID for easier tracking, exists in the Linux kernel’s RDS (Reliable Datagram Sockets) and was patched earlier this month.
“PinTheft is a Linux local privilege escalation exploit for an RDS zerocopy double-free that can be turned into a page-cache overwrite through io_uring fixed buffers,” V12 said in a Tuesday advisory.
When security researchers want to understand what a modern processor is really doing with the kind of detail that determines whether attacks like Spectre and Meltdown are possible, they usually run their experiments on top of an operating system that was never built for the job. They open up macOS or Linux, patch the kernel by hand, and hope the modifications hold. The approach is unstable, hard to reproduce, and on Apple’s platforms, slated for deprecation.
A team at MIT’s Computer Science and Artificial Intelligence Laboratory (CSAIL) decided to build something different. Fractal, a new operating system kernel written from the ground up, treats the hardware itself as the object of study. Its first major use, a deep look at the branch predictors (CPU’s way of guessing what code to run next before it knows for certain), so it doesn’t have to waste time waiting to find out) inside Apple’s M1 processor, has already turned up findings that prior work missed, including the first evidence that a class of speculative attack known as “Phantom” affects Apple Silicon.
“We’re using hardware in ways it wasn’t designed for,” says Joseph Ravichandran, the MIT PhD student who led the project. “It’s not even obvious that this is a possible thing you could do with the hardware. But we found a way to pull all these different primitives off. It’s like a microscope. If you’ve got a hand magnifying glass, you can see a little bit. But if you had an electron microscope, now we’re really talking. That’s what Fractal is. The electron microscope of operating systems.”