Ultra-intense ultrashort lasers have a wide-ranging scope of applications, encompassing basic physics, national security, industrial service, and health care. In basic physics, such lasers have become a powerful tool for researching strong-field laser physics, especially for laser-driven radiation sources, laser particle acceleration, vacuum quantum electrodynamics, and more.
A dramatic increase in peak laser power, from the 1996 1-petawatt “Nova” to the 2017 10-petawatt “Shanghai Super-intense Ultrafast Laser Facility” (SULF) and the 2019 10-petawatt “Extreme Light Infrastructure—Nuclear Physics” (ELI-NP), is due to a shift in gain medium for large-aperture lasers (from neodymium-doped glass to titanium:sapphire crystal). That shift reduced the pulse duration of high-energy lasers from around 500 femtoseconds (fs) to around 25 fs.
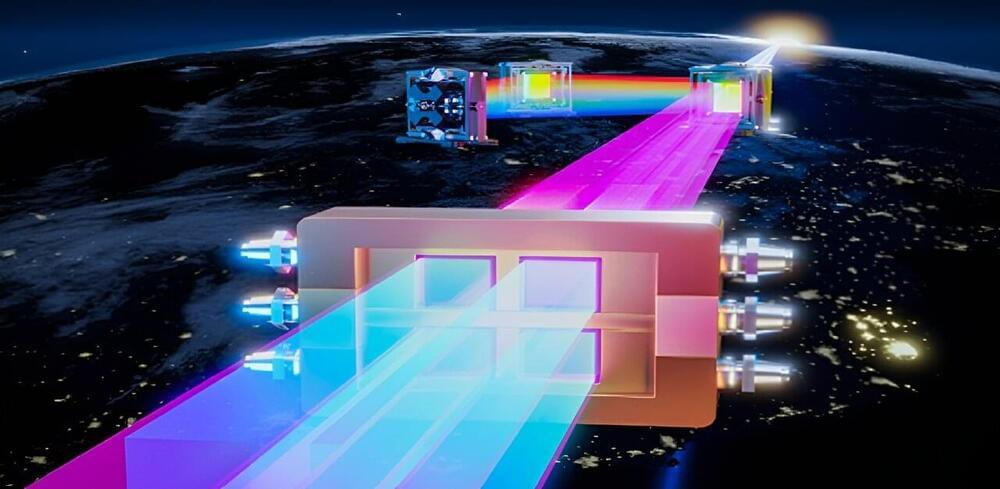
However, the upper limit for titanium: sapphire ultra-intense ultrashort lasers appears to be 10-petawatt. Presently, for 10-petawatt to 100-petawatt development planning, researchers generally abandon the titanium: sapphire chirped pulse amplification technology, and turn to optical parametric chirped pulse amplification technology, based on deuterated potassium dihydrogen phosphate nonlinear crystals. That technology, due to its low pump-to-signal conversion efficiency and poor spatiotemporal-spectral-energy stability, will pose a great challenge for the realization and application of the future 10–100 petawatt lasers.