Cisco released fixes for CVE-2025–20393, a CVSS 10.0 zero-day RCE flaw in AsyncOS exploited by a China-linked APT via email security appliances.



Microsoft is investigating widespread reports that a January Windows 11 security update is causing the classic Outlook desktop client to freeze and hang for users with POP email accounts.
POP (Post Office Protocol) is an email retrieval protocol used for downloading emails from a server to a local device. While POP isn’t as widely used as IMAP or Exchange, it is still popular among home users and small businesses.
This known issue affects users who have installed the KB5074109 security update for Windows 11 25H2 and 24H2, with those impacted reporting that classic Outlook does not exit properly and will not restart after being closed.
The Age of Abundance: AGI Predictions and Investment Strategy for 2026 ## The imminent emergence of Artificial General Intelligence (AGI) will significantly impact investment strategies, and investors should prepare by accumulating valuable assets, diversifying their portfolios, and adopting a strategic investment approach to capitalize on the growth potential of AGI and the resulting Age of Abundance ##
## Questions to inspire discussion.
Investment Strategy.
🎯 Q: How should I build an investment portfolio for the AGI era? A: Focus on companies with best management and growth potential in AGI, robotics, and space industries using dollar-cost averaging strategy to systematically build positions over time rather than lump-sum investing.
💰 Q: What alternative assets should I accumulate for security during AGI transition? A: Accumulate gold, silver, and Bitcoin as modern safe havens to protect wealth during periods of change and uncertainty as traditional financial systems adapt to AGI disruption.
🏢 Q: Why should real estate be overweighted in an AGI-focused portfolio? A: Overweight real estate compared to company ownership and reserves because AGI and robotics industries will require physical space for operations, data centers, and manufacturing facilities.

Node.js has released updates to fix what it described as a critical security issue impacting “virtually every production Node.js app” that, if successfully exploited, could trigger a denial-of-service (DoS) condition.
“Node.js/V8 makes a best-effort attempt to recover from stack space exhaustion with a catchable error, which frameworks have come to rely on for service availability,” Node.js’s Matteo Collina and Joyee Cheung said in a Tuesday bulletin.
“A bug that only reproduces when async_hooks are used would break this attempt, causing Node.js to exit with 7 directly without throwing a catchable error when recursions in user code exhaust the stack space. This makes applications whose recursion depth is controlled by unsanitized input vulnerable to denial-of-service attacks.”

Microsoft has resolved a known issue that was causing security applications to incorrectly flag a core Windows component, the company said in a service alert posted this week.
The list of affected systems is quite extensive and includes both client (Windows 10 and Windows 11) and server (Windows Server 2012 through Windows Server 2025) platforms.
According to widespread user reports over the past several months, third-party security software flagged Windows assets, including WinSqlite3.dll, a dynamic link library (DLL) included with the Windows system libraries that implements the SQLite database engine, as vulnerable to attacks exploiting a memory corruption vulnerability (CVE-2025–6965).
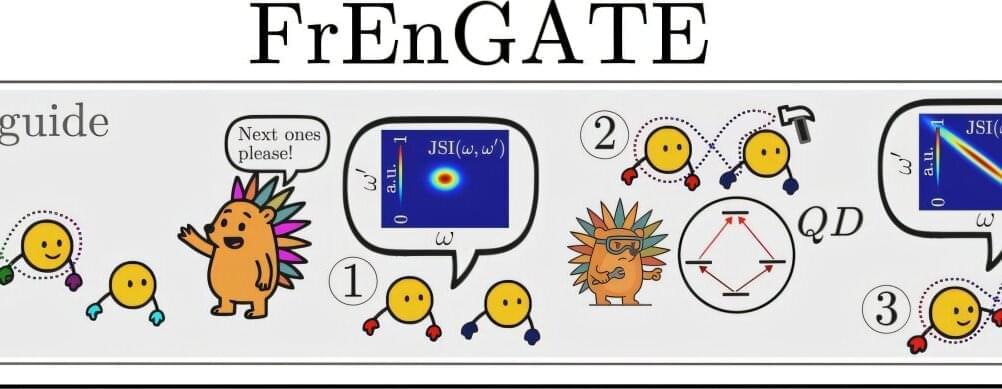
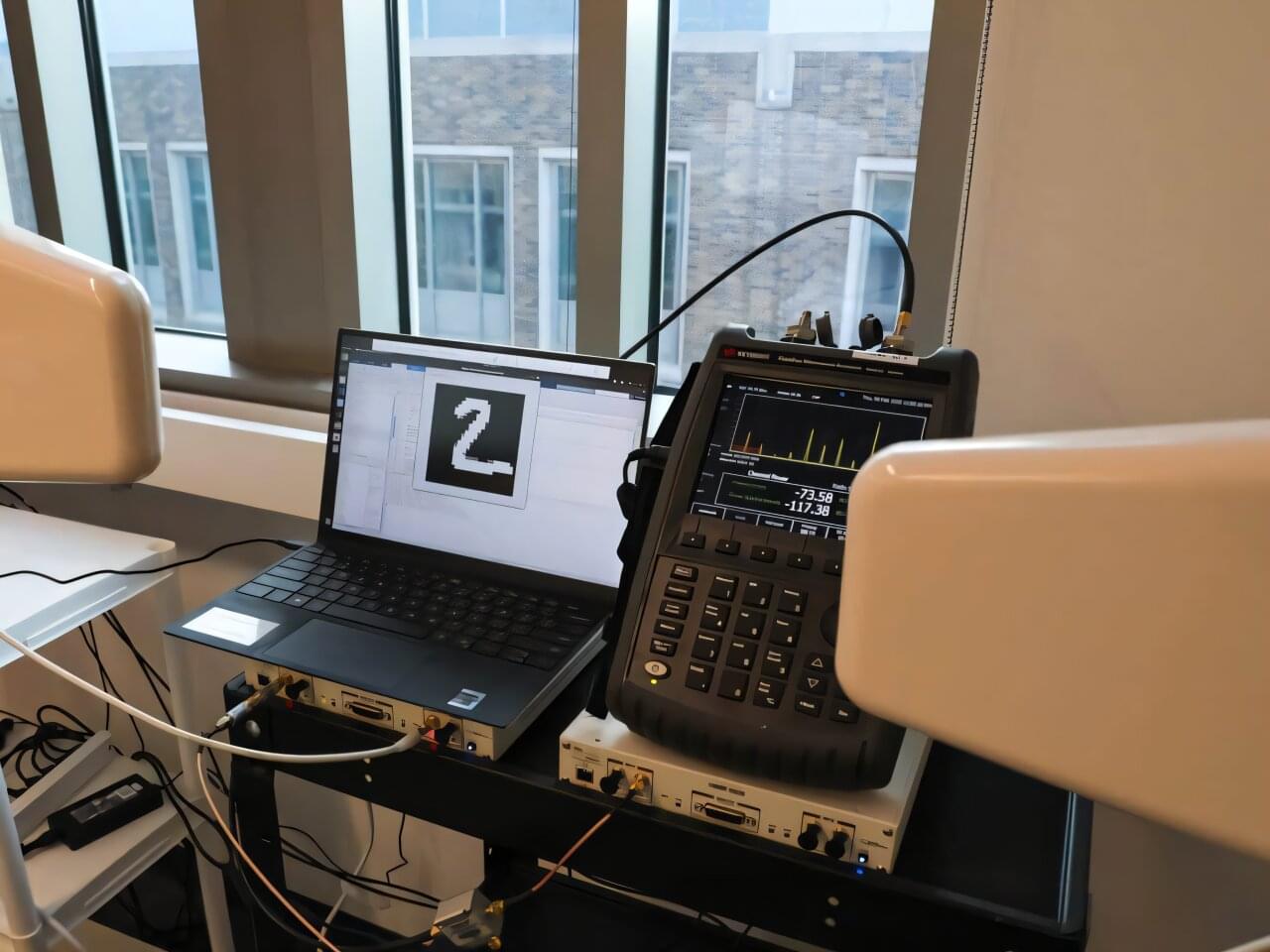
Researchers have designed a new device that can efficiently create multiple frequency-entangled photons, a feat that cannot be achieved with today’s optical devices. The new approach could open a path to more powerful quantum communication and computing technologies.
“Entangling particles efficiently is a critical capability for unlocking the full power of quantum technologies—whether to accelerate computations, surpass fundamental limits in precision measurement, or guarantee unbreakable security using the laws of quantum physics,” said Nicolas Fabre from Telecom Paris at the Institut Polytechnique de Paris.
“Photons are ideal because they can travel long distances through optical fibers or free space; however, there hasn’t been a way to efficiently generate frequency entanglement between more than two photons.”

To learn more about the non-security updates released today, you can review our dedicated articles on the Windows 11 KB5074109 & KB5073455 cumulative updates and Windows 10 KB5073724 extended security update.
This month’s Patch Tuesday fixes one actively exploited and two publicly disclosed zero-day vulnerabilities.
As drones survey forests, robots navigate warehouses and sensors monitor city streets, more of the world’s decision-making is occurring autonomously on the edge—on the small devices that gather information at the ends of much larger networks.
But making that shift to edge computing is harder than it seems. Although artificial intelligence (AI) models continue to grow larger and smarter, the hardware inside these devices remains tiny.
Engineers typically have two options, neither are ideal. Storing an entire AI model on the device requires significant memory, data movement and computing power that drains batteries. Offloading the model to the cloud avoids those hardware constraints, but the back-and-forth introduces lag, burns energy and presents security risks.
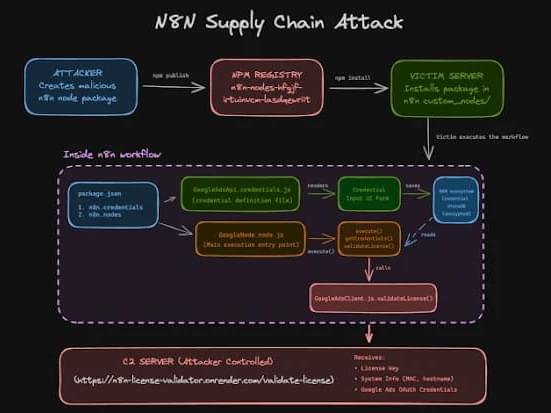
N8n has also warned about the security risk arising from the use of community nodes from npm, which it said can introduce breaking changes or execute malicious actions on the machine that the service runs on. On self-hosted n8n instances, it’s advised to disable community nodes by setting N8N_COMMUNITY_PACKAGES_ENABLED to false.
“Community nodes run with the same level of access as n8n itself. They can read environment variables, access the file system, make outbound network requests, and, most critically, receive decrypted API keys and OAuth tokens during workflow execution,” researchers Kiran Raj and Henrik Plate said. “There is no sandboxing or isolation between node code and the n8n runtime.”
“Because of this, a single malicious npm package is enough to gain deep visibility into workflows, steal credentials, and communicate externally without raising immediate suspicion. For attackers, the npm supply chain offers a quiet and highly effective entry point into n8n environments.”