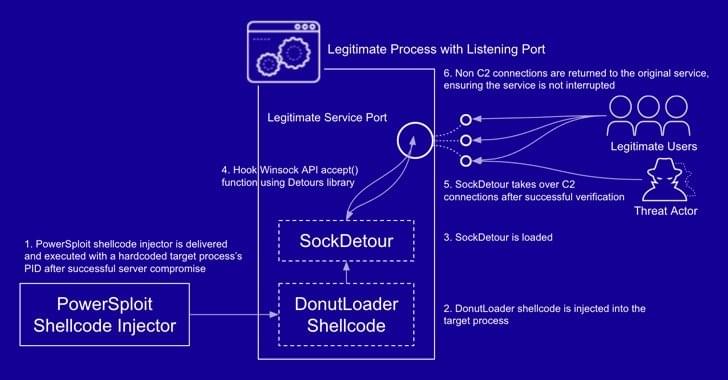
The publication in the Military-Industrial Kurier (VPK) on February 26, 2013, of an article by the Russian Chief of the General Staff, General Valery Gerasimov, entitled “The Value of Science in Foresight” [in Russian], has been seen by some analysts as a turning point in Russian military doctrine and the beginning of an explicit strategy of hybrid warfare. Indeed, information and cyber operations were an integral feature of Russia’s annexation of the Crimean Peninsula in 2014. Yet, the principal thesis of Gerasimov’s article is that alternative methods of conflict can be found to offset asymmetric disadvantages created by a superior enemy force. Such methods demand the application of the entire military-industrial complex to yield innovations in technology and tactics – the results of which can be seen in the proliferation of APT actors and computational propaganda operations observed by Western countries and their allies.
While we can only hope for a rapid cessation of the fighting in Ukraine, the consequences of Russian military intervention will extend far beyond the battlefield in years to come. Renewed focus and accelerated innovation and adoption of new technologies to protect the data and applications that Western societies depend on is now an imperative, not a choice – this is Gerasimov’s lesson.
The distinctions between war and peace, combatant and civilian, state actor and criminal proxy, are blurred in what has been termed the “fifth domain” of military operations. Collective cybersecurity in response to the increased prospect of cyberattack will demand not only political leadership, international cooperation, and industrial collaboration, but also the active participation of companies and individuals in the manner of civil defense, reminiscent of the Cold War. With the change in the world order brought about by Russia’s military action in Ukraine, we are all now standing on the frontline of cybersecurity.