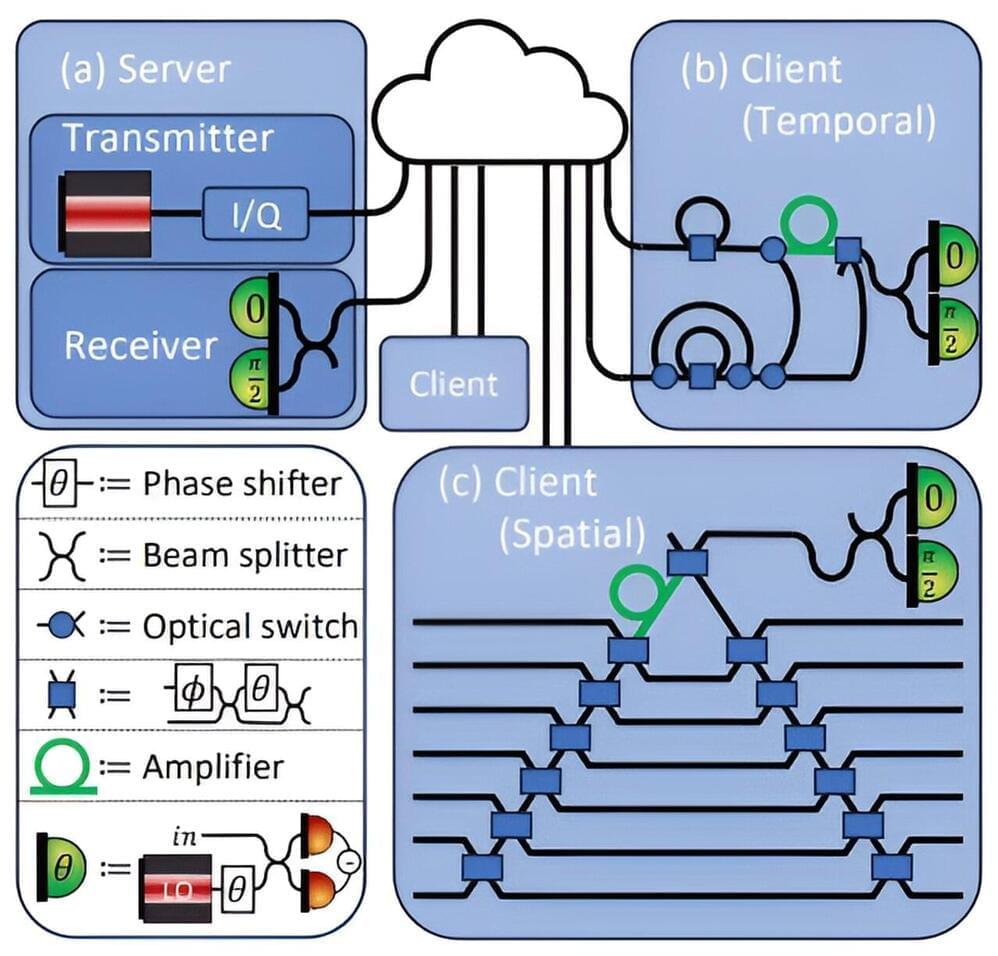
Quantum computers and quantum communication are groundbreaking technologies that enable faster and more secure data processing and transmission compared to traditional computers. In quantum computers, qubits serve as the fundamental units of information, functioning as the quantum mechanical equivalent of bits in classical computing.
Where, for example, laser pulses in a glass fiber transport information from A to B in classical digital communication, quantum mechanics uses individual photons. In principle, this makes it impossible to intercept the transmitted data. Qubits that are optically addressable (can be controlled or read out with light) are suitable for storing the photons’ information and processing it in quantum computers. The qubits can store and process quantum states, and absorb and emit them in the form of photons.