It is a common hack to stretch a balloon out to make it easier to inflate. When the balloon stretches, the width crosswise shrinks to the size of a string. Noah Stocek, a PhD student collaborating with Western University physicist Giovanni Fanchini, has developed a new nanomaterial that demonstrates the opposite of this phenomenon.
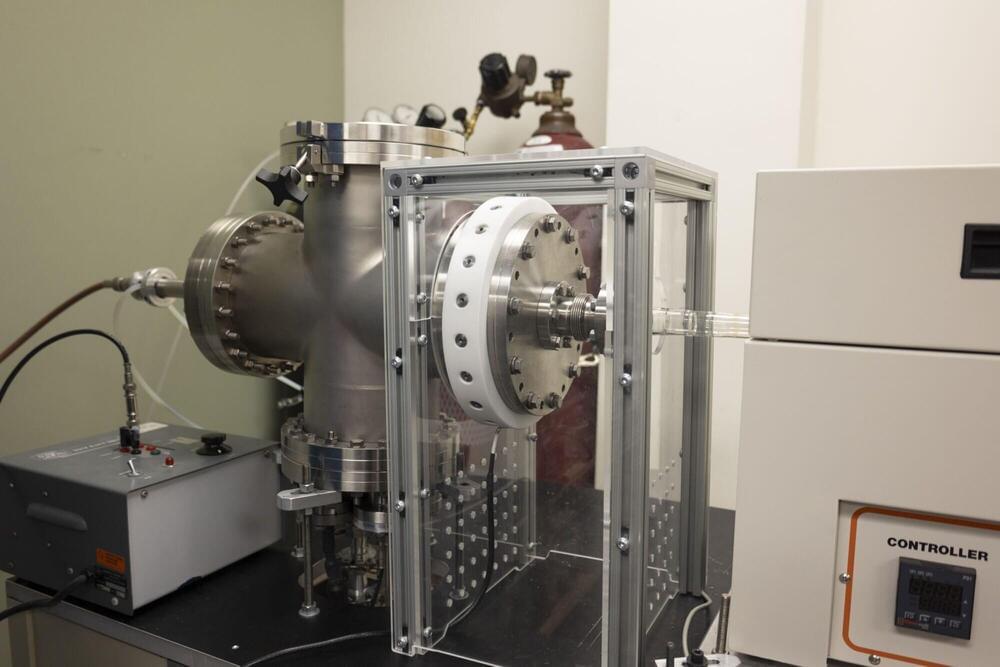
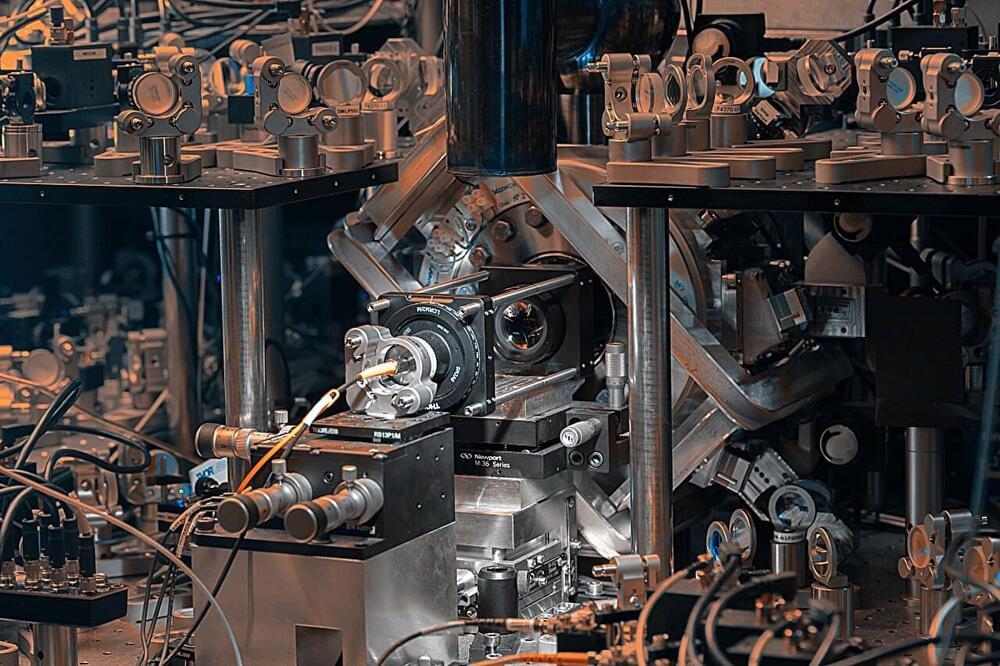
Working at Interface Science Western, home of the Tandetron Accelerator Facility, Stocek, and Fanchini formulated two-dimensional nanosheets of tungsten semi-carbide (or W2C, a chemical compound containing equal parts of tungsten and carbon atoms) which when stretched in one direction, expand perpendicular to the applied force. This structural design is known as auxetics.